Best Practices in Online Teaching Training Best practices such as teacher presence, timely teacher feedback, varied assessments, collaborative work, etc. do have an impact on online teaching and learning. Best Practices...
The Future of Work Online Collaboration Discussion
The Future of Work Online Collaboration Discussion As we leave behind old working practices to meet new demands in the workplace virtual factors need to be analyzed. Online collaboration has become the new normal for...
Frequently Asked Questions About Dyslexia MVC
Frequently Asked Questions About Dyslexia MVC Here is a summary covering questions about Dyslexia. Read Frequently Asked Questions About Dyslexia MVC. What is dyslexia? Dyslexia is a language-based learning...
How To Manage and Maintain your Computer read
How To Manage and Maintain your Computer read How To Manage and Maintain your Computer read. Here’s some critical thinking presented in A Guide to Managing and Maintaining your computer. This list is not...
Writing 3 Ways to Build a Story Characters
Writing 3 Ways to Build Story Characters Incorporating a Character into a Workable Plot Writing 3 Ways to Build Story Characters. Characters form a strong connection with your audience. Having a notable character is a...
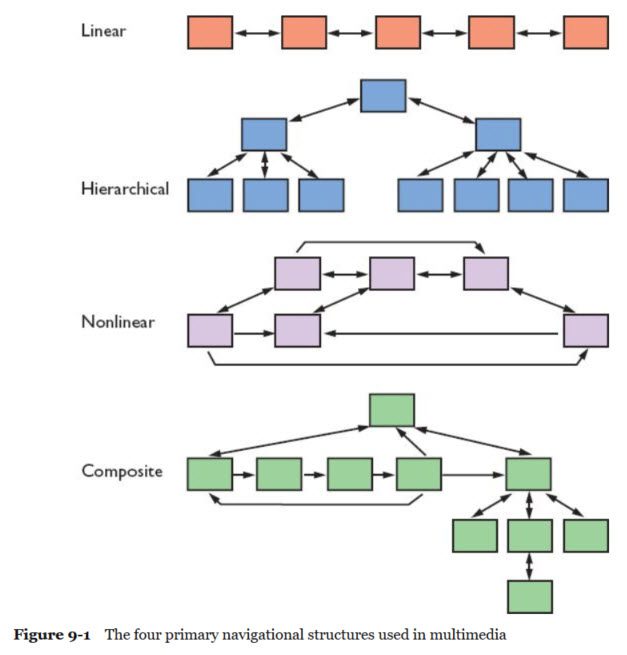
Game Design: Documentation Vision for the Game
Game Design: Documentation Vision for the Game In a series of posts over the next months I will cover some of the core components that are core to Game Design. In these posts, we will explore Game Design: Documentation...
Systems Analysis and Design A Preview For a Student
Systems Analysis and Design A Preview For a Student Here’s an overview for any adult learner specializing in Systems Analysis and Design A Preview For a Student. Many corporation entities add or load...
Home and Small Business Security in Your Network
Home and Small Business Security in Your Network There are several strategies that can be employed for both home and professional networks. Anyone of these techniques and strategies should be considered depending...
Mobile Device Threats and Security Risks Usage
Mobile Device Threats and Security Risks Usage There are many threats and security risks including the devices. So where do we start today? Mobile Device Threats and Security Risks Usage. Editor note: This post has...
Use Both Sides of Your Brain Book Critique
Use Both Sides of Your Brain Book Critique Summary: Use Both Sides of Your Brain by Tony Buzan published by Penguin Group, Toronto Canada in 1974. Use Both Sides of Your Brain Book Critique. Shows concrete...
Essay Writing Analyzing the Question Key Terms
Essay Writing Analyzing the Question Key Terms Here we present ideas on how to analyze the question and key terms in Essay Writing Analyzing the Question Key Terms. Analyzing the Question Understanding the question...
How To Make A Website For Your Market read
How To Make A Website For Your Market read Making a website for your business combines the idea of your service or product and the social networking power of the internet. If your in charge of the business’...
Strategic Management – Reasons Systems Projects
Strategic Management – Reasons Systems Projects A systems request is a formal way of asking for IT support. Read about Strategic Management – Reasons Systems Projects below. Previous post: Strategic Planning...
Writing An Essay Understanding the Question read
Writing An Essay Understanding the Question read Understanding the Question. In the first step in essay writing you will analyze the essay task, what the topic is, and also give an indication of what kind of things you...
Adult Learning The End of Life for Flash in education
Adult Learning The End of Life for Flash in education Here is a quick snapshot of changes coming at the end of 2020 to Adobe Flash, education and e-learning environments including both business and students. Adult...
Content Writing Course Available Now read
Blog Posts Content Writing Course Available Now read In an online class, the experience requires the learner to be dedicated, committed, and disciplined in order to be successful. Content Writing Course Offering Now...
Operating System privacy and security issues
Operating System privacy and security issues You may or may not know that operating systems have built-in safety features, such as a firewall, antivirus, antimalware claimed protection. There are numerous brands and...